The digital lives we’ve built for ourselves are proving to be more vulnerable to cyber attacks than ever before. Tech, media, and, yes, even beef corporations are being infiltrated by sophisticated hacker groups which current cyber solutions seemingly can’t defend against. Gone are the days of exclusively feeling nervous about physical break-ins — today’s main security concerns are digital. At Seedcamp, we have been backing a variety of companies looking to keep people’s personal and professional lives safe. One example is Zamna, which is focused on traveler health verification at airports (talk about a timely problem to solve!). Another is Cyscale, one of our most recent additions to the Seedcamp Nation, which maps, secures, and monitors cloud assets for companies. Whether in a professional or personal setting, we are passionate about digital security due to its ever-increasing importance to make our world a safer place.
Today, two big trends are putting strain on our old ways of securing data, infrastructure, and applications. These are 1) the COVID-induced move to a remote workforce and 2) a shift to open-source and web3.
Let’s dig in.
From work-bound to house-bound.
First of all, and as no news to anyone, COVID has made the work-bound, house-bound. Our remote workforce comes with a myriad of dangers as today’s employees rely on home networks, which oftentimes aren’t secured. When workers are decentralised and operate from multiple different locations, one hack on a personal network can lead to the entire organisation being at risk. In short, the number of open doors hackers can walk through to infiltrate a company has dramatically increased. Furthermore, WFH has blurred the lines between personal devices and work devices. How often do you turn on your personal laptop to check work emails? How frequently do you use your personal mobile device to do a two-factor authentication or log into a Zoom meeting? Every time this line blurs further, cyber risks become greater.
From Web2 to Web3.
Second of all, we are experiencing the rise of Web3 across the digital world. If you’re reading this, then you are a participant of Web2, our interactive social web. What differentiates Web2 and Web3 is the decentralised nature of Web3. Developers building on this new iteration of the web don’t deploy applications that run on single servers. Rather, applications run on blockchains, decentralised networks of many peer-to-peer nodes, making Web3 verifiable, trustless, self-governing, and permissionless. Emre Baran, the co-founder of Seedcamp portfolio company Cerbos and our in-house wizard about all things security, thinks that the future of cyber will operate under a zero-trust security model. Web3 is the lever but also an enabler of this future. It exposes everything that was traditionally under the hood.
Web3 is almost entirely open-source. At Seedcamp, we believe strongly that open-source is here to stay; from a fundamental lever, it simply doesn’t make sense for businesses to spend a ton of money to develop something that is free and open to use. That said, open-source also creates cybersecurity concerns that are being severely underlooked. Given that no one owns what is open-source, there is no custodian for it. No one protects it. Additionally, because businesses are stacking one open-source solution onto another when building their products, hackers tampering one layer results in the insecurity of the entire stack. Adam Nygate, the founder and CEO of Seedcamp portfolio company 418sec occupies himself with just this issue. In a recent interview, we asked him about the cyber threats of the shift to open-source:
Breaking down cyber.
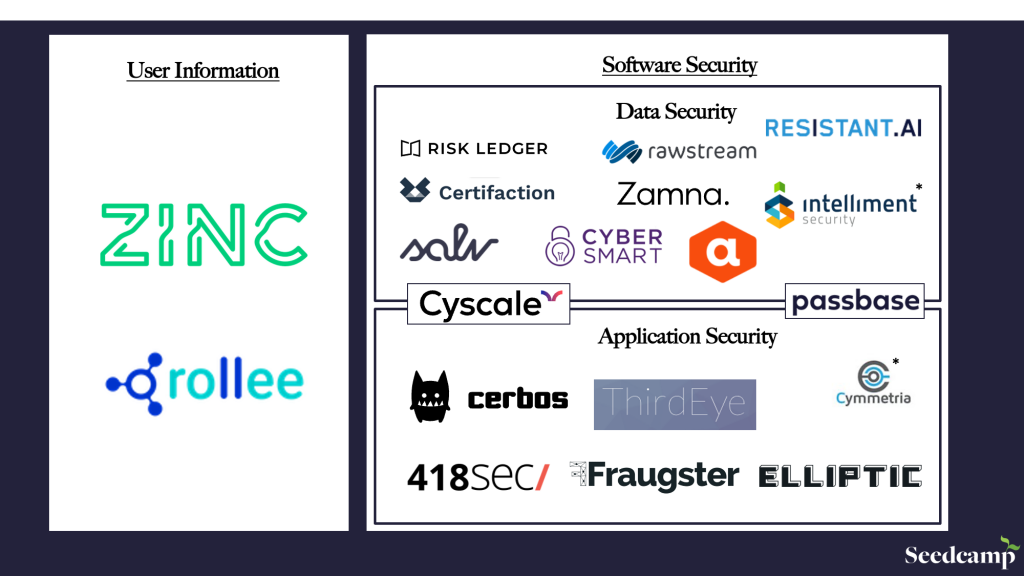
Work from home and Web3 represent two seismic shifts in cybersecurity and we are excited to see what’s next for this massive market. At Seedcamp, we break down the cybersecurity space into two large segments, namely security focused on 1) software and 2) user information
Software Security
Software security protects against malicious attacks and other hacker risks that may prevent software from functioning correctly. Software security is innately proactive — in other words, it defines everything an engineer would do pre-deployment in order to ensure safety from cyber attacks. This includes secure software design, user authentication, user session management, validation of third-party software, and secure coding guidelines.
One subset of software security is application security, which is the layer that is most vulnerable to cyber-attacks. Just as software security deals with cybersecurity pre-deployment, application security is focused on maintaining security post-deployment. This includes monitoring of programmes and malicious code detection, to name just two. When a cyberthreat wreaks havoc on a system, engineers can tap into the application layer to detect the source, patch the problem, and upgrade to a new system. Software is more static; once something is deployed, it is very costly to cyber-proof oneself by re-rigging the software rather than the application.
The second subset of software security is data security. Data security deals with the process of protecting data, in use and in motion, from data corruption and unauthorized entities. Encrypting or tokenizing data are two common ways to protect data, whether in a data lake, in the cloud, on a mobile device, or on hardware. Data security transcends the entire OSI stack of a company, from the presentation layer (where encryption occurs) all the way down to the transport layer and data link layer.
User Information Security
While data security deals with data moving through the OSI stack, user information security deals with what we like to call the ‘8th layer of the OSI”. The 8th layer is the human one; it deals with the people operating in your company. Let’s take one step back. Hackers can hack in a variety of ways. One approach is physically walking through your company’s doors and cutting a cable. Another is hacking into your network or application. But what happens when the hacker works at your company or is a customer of yours? How do you protect the human layer of your company’s security stack? This is where user information security comes into play. Likely the most imperfect security layer of them all, user information security attempts to ensure your hires, partners, and customers are who they say they are via background checks and employment data verification. Companies do their very best to defend against internal threats but it’s impossible to get 100% assurance. Companies protect the 7 layers of the OSI and hope to protect the 8th.
Seedcamp founder Ali Hamriti knows a thing or two about user information. He is the co-founder and CEO of Rollee, a platform for employment data. Rollee lets brokers and fintechs verify their customers’ employment and income data and, as a result, prevent fraud and make better decisions. We asked Ali about his views on the future of cybersecurity:
What we are looking for in the next breakthrough cyber company.
We are entering an era of zero-trust cybersecurity. Given the decentralised nature of the future web and our increasing dependence on digital identities, companies are realising that nothing in the cyber world can be left up to chance. We’ve been fortunate enough to have backed some exceptional founders leading the way in the cybersecurity vertical (and if you’re building something with the ambition to truly redefine cyber, please get in touch and apply for funding here!). But, of course, our search for Europe’s breakthrough cybersecurity companies doesn’t stop with this list. We are excited to see how entrepreneurs think about protecting a future which is more dependent on digital identities, via Web3 and WFH. Whether on the user information or software security side of things, we are excited for what’s in store.
The Seedcamp Cybersecurity Portfolio
If you’re working on something interesting in cybersecurity, apply here or email us at funding@seedcamp.com. Additionally, if you’re looking for opportunities to work in this exciting space, feel free to check out our portfolio job board here.
Seedcamp’s Cybersecurity Footprint (so far…)
- 418sec: Securing the world’s open-source code
- Cyscale: Complete cloud visibility & control platform
- Cerbos: Authorization as a Service platform
- Certifaction: Restoring trust in the digital world by creating instantly verifiable information on the blockchain
- Cybersmart: Automated compliance to protect your organisation and data
- Cymmetria: Using Virtual Machines To Decoy And Detect Hackers
- Elliptic: Identifying illicit activity on the blockchain
- Fraugster: Using AI to eliminate e-commerce fraud and increase customers’ profits
- Passbase: Developer-friendly identity verification tools
- Risk Ledger: The world’s first scalable security assurance platform
- Salv: Smart AML platform for banks & fintechs
- ThirdEye: Intelligent computer vision software that understands every single physical interaction and tracks every shelf in your store
- Rawstream: The Fastest, Simplest Web Filter In The Cloud
- ResistantAI: Protecting automated financial systems from manipulation and attack
- Rollee: The gateway for reliable employment and income data
- Zamna: Strategic data sharing for airlines, enabled through blockchain
- Zinc: Automated reference and background checking